|
|
What is 'Trojan Horse'?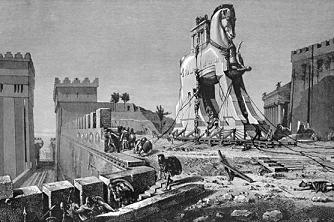 The original Trojan Horse was a huge, hollow wooden horse constructed by the Greeks to gain entrance into the City of Troy during the Trojan War in the 12th or 13th century B.C. The 10 year long Trojan war ended when the Greeks feigned defeat and withdrew to a nearby island, leaving the giant wooden horse behind. Unbeknown to the Trojans, the horse was hollow and concealed some Greek soldiers. The horse was brought inside the city walls of Troy and during the night, the soldiers dropped out of its belly and opened the city gates, so that the rest of the Greek army could enter the city. Thus, the Greeks took the city of Troy and ended the Trojan wars. The original Trojan Horse was a huge, hollow wooden horse constructed by the Greeks to gain entrance into the City of Troy during the Trojan War in the 12th or 13th century B.C. The 10 year long Trojan war ended when the Greeks feigned defeat and withdrew to a nearby island, leaving the giant wooden horse behind. Unbeknown to the Trojans, the horse was hollow and concealed some Greek soldiers. The horse was brought inside the city walls of Troy and during the night, the soldiers dropped out of its belly and opened the city gates, so that the rest of the Greek army could enter the city. Thus, the Greeks took the city of Troy and ended the Trojan wars.
In computing terms, a Trojan Horse is a program that looks like a legitimate program, but includes some malicious programming. Usually, the attacker places the trojan horse on the attacked computer (or filesystem), and it requires an action (such as double-clicking) by the user to activate the trojan horse. It may be that the user becomes aware of the trojan horse at this point, when the trojan horse does not function in the same way as the program that was expected.
However, it is probably more dangerous when the trojan horse does appear to operate in the way that is expected. That way, the malicious program can continue to operate undetected, and it may be some time before it is discovered.
Other Terms
|
|





